Time limit: 0
Quiz Summary
0 of 70 Questions completed
Questions:
Information
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading…
You must sign in or sign up to start the quiz.
You must first complete the following:
Results
Quiz complete. Results are being recorded.
Results
0 of 70 Questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 point(s), (0)
Earned Point(s): 0 of 0, (0)
0 Essay(s) Pending (Possible Point(s): 0)
Categories
- Not categorized 0%
-
Unfortunately, you didn’t pass the practice exam, but hey, you have unlimited access.😎
Practice makes you perfect! 👊 -
Congratulations! 🥳
You have passed the practice exam successfully! You are one step closer to pass the real exam!
We hope to see you again on another certification path.✌️
Good luck with the exam! Stay strong.👊
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- Current
- Review
- Answered
- Correct
- Incorrect
-
Question 1 of 70
1. Question
What is the network ID associated with the host located at 192.168.0.4/26?
CorrectIncorrect -
Question 2 of 70
2. Question
An organization requires the use of a central computer to collect and distribute emails to networked devices inside the organization. The central computer will deliver emails through SMTP using port 465. Which of the following network types is MOST suitable in this case?
CorrectIncorrect -
Question 3 of 70
3. Question
A network technician is connecting two separate networks by configuring the interface of the routers. The new network has an IP of 30.40.50.4/30. Which of the following IPs does the technician need to assign to the routers?
CorrectIncorrect -
Question 4 of 70
4. Question
Which of the following cloud deployment models is MOST suitable for government entities that share similar requirements related to security levels, audit, and privacy?
CorrectIncorrect -
Question 5 of 70
5. Question
You are planning to design a network where each node should be directly connected to every other node. Which of the following network topologies is MOST suitable for this design?
CorrectIncorrect -
Question 6 of 70
6. Question
Which of the following ports is used by HTTPS by default?
CorrectIncorrect -
Question 7 of 70
7. Question
Which of the following layers in a Software-Defined Network (SDN) architecture manages policies and traffic flow?
CorrectIncorrect -
Question 8 of 70
8. Question
Nick has been hired to configure the firewall of the ACME Corporation. He needs to allow customers to visit their web pages over a secure connection. Which of the following ports must be allowed through the firewall?
CorrectIncorrect -
Question 9 of 70
9. Question
Drag and drop the various 802.11 wireless standards into their respective frequencies.
Sort elements
- 802.11g
- 802.11a
- 802.11n
-
2.4 GHz
-
5 GHz
-
2.4 GHz / 5 GHz
CorrectIncorrect -
Question 10 of 70
10. Question
A network technician is tasked with configuring the firewall of your organization. You need to block employees to use Telnet to connect remotely to your servers. What port must be blocked through the firewall?
CorrectIncorrect -
Question 11 of 70
11. Question
What is the broadcast address associated with the host located at 40.20.3.2/30?
CorrectIncorrect -
Question 12 of 70
12. Question
A network engineer designs a Local Area Network (LAN) for a new office. He needs to determine the devices and the cabling to create a star topology. Which layer of the (OSI) model defines electrical specifications for cabling and devices?
CorrectIncorrect -
Question 13 of 70
13. Question
Which of the following service models allows users to connect to and use cloud-based apps over the Internet?
CorrectIncorrect -
Question 14 of 70
14. Question
Which of the following IPs are private networks? (Select TWO).
CorrectIncorrect -
Question 15 of 70
15. Question
What is the CIDR notation for a new IT department’s subnet that requires allocating 9 addresses?
CorrectIncorrect -
Question 16 of 70
16. Question
A network technician has been notified that the routing protocol which is used to distribute IP routing information throughout a single Autonomous System (AS) in an IP network needs troubleshooting. Which of the following routing protocols should the technician be familiar with?
CorrectIncorrect -
Question 17 of 70
17. Question
Which of the following routing protocols creates network stability by guaranteeing routers can adapt to route failures?
CorrectIncorrect -
Question 18 of 70
18. Question
A network technician has been notified that an available wireless device is using 2.4 GHz and has been asked to install a new 5 GHz wireless device on the existing network to prevent interference. Which of the following 802.11 standards should the technician install to provide a 5 GHz wireless network?
CorrectIncorrect -
Question 19 of 70
19. Question
Which of the following type of wireless networks uses the 5 GHz frequency band and reaches speeds of up to 7 Gbps?
CorrectIncorrect -
Question 20 of 70
20. Question
Which of the following 802.11 wireless standards are able to use Multiple Input, Multiple Output (MIMO) technology? (Select TWO)
CorrectIncorrect -
Question 21 of 70
21. Question
Which of the following 802.11 standards uses the 5 GHz frequency band and reaches maximum link rates of up to 600 Mbps?
CorrectIncorrect -
Question 22 of 70
22. Question
Which of the following features helps network engineers and administrators to analyze and debug data and/or diagnose errors on a network?
CorrectIncorrect -
Question 23 of 70
23. Question
Which type of antenna improves transmission and reception of communications and reduces interference?
CorrectIncorrect -
Question 24 of 70
24. Question
Which of the following networking standards supports virtual LANs (VLANs) on an IEEE 802.3 Ethernet network?
CorrectIncorrect -
Question 25 of 70
25. Question
Which of the following encryption standards is considered the most secure method of protecting Wi-Fi networks?
CorrectIncorrect -
Question 26 of 70
26. Question
Which of the following standards should be used to provide power to VoIP phones with LCD and video conference abilities without the need for power adapters?
CorrectIncorrect -
Question 27 of 70
27. Question
A network technician is tasked with installing a new wireless network that utilizes the 2.4 GHz and/or 5 GHz radio frequency bands and reaches a maximum link rate of 9 Gbps. Which of the following 802.11 standards does the technician need to configure to meet the requirements?
CorrectIncorrect -
Question 28 of 70
28. Question
Which of the following should be used to allow a computer to keep running for a short time when the primary power source is lost?
CorrectIncorrect -
Question 29 of 70
29. Question
Drag and drop the disaster recovery terms into their respective fields.
Sort elements
- RPO
- RTO
- MTTR
- MTBF
-
A period of time in which an enterprise’s operations must be restored following a disruptive event
-
A maximum tolerable length of time that a computer or system can be down after a failure occurs
-
The average time it takes to repair and restore a component or system to function
-
The average time that equipment is operating between breakdowns or stoppages
CorrectIncorrect -
Question 30 of 70
30. Question
Students of ExamsDigest report that they aren’t able to access the website. Upon investigation of the cause, it is discovered that the server was down. Which of the following concept would BEST ensure that the website remains up and running without interruptions?
CorrectIncorrect -
Question 31 of 70
31. Question
An organization set up a new server last year. The server was operational for 1,000 hours and broke down 10 times that year. Which of the following would BEST represent the MTBF of the server?
CorrectIncorrect -
Question 32 of 70
32. Question
Which of the following is NOT considered an SNMP component?
CorrectIncorrect -
Question 33 of 70
33. Question
Which of the following types of agreements creates a confidential relationship between two or more parties to protect any type of confidential and proprietary information?
CorrectIncorrect -
Question 34 of 70
34. Question
One purpose of a site survey is to:
CorrectIncorrect -
Question 35 of 70
35. Question
Which of the following network performance metrics measures the time it takes for data to get to its destination across the network?
CorrectIncorrect -
Question 36 of 70
36. Question
Users within an office building report network connectivity issues. A technician troubleshooting the issue notices there are faulty cables in the server room which connect the core and distribution layer. Which of the following is causing the issue?
CorrectIncorrect -
Question 37 of 70
37. Question
A network technician is connecting to a Cisco switch to check the status of the interfaces. After typing, the
show interfacecommand he notices there are 259429 CRC errors on the interface FastEthernet0/13. Which of the following is MOST likely the issue?CorrectIncorrect -
Question 38 of 70
38. Question
A technician is called to block certain computers from connecting to the Wi-Fi network. The computers that need to be blocked have the following MAC addresses:
- Computer A: 00:00:5e:00:53:af
- Computer B: aa:55:5e:00:53:af
- Computer C: 44:20:5e:00:53:af
Which of the following tools does the technician need to complete the task?
CorrectIncorrect -
Question 39 of 70
39. Question
Exploits are a weakness in software systems, while vulnerabilities are attacks made to take advantage of exploits.
CorrectIncorrect -
Question 40 of 70
40. Question
Which one of the following attacks requires the attacker to be on the same network as the victim?
CorrectIncorrect -
Question 41 of 70
41. Question
Which of the following statements are true regarding Security Information and Event Management (SIEM)? (Select TWO)
CorrectIncorrect -
Question 42 of 70
42. Question
A graduate intern asked you to explain to him what is zero-day vulnerability all about. Which of the following statements is true?
CorrectIncorrect -
Question 43 of 70
43. Question
Which of the following options are considered authentication protocols? (Select TWO)
CorrectIncorrect -
Question 44 of 70
44. Question
Your website uses Cloudflare to resolve DNS queries. Upon checking the records, you have discovered there are A and MX record entries that point to unknown and potentially harmful IP addresses. Which of the following attacks have you just discovered?
CorrectIncorrect -
Question 45 of 70
45. Question
In which of the following wireless network attacks does the attacker set up a fraudulent Wi-Fi access point that appears to be legitimate but is used to eavesdrop on wireless communications?
CorrectIncorrect -
Question 46 of 70
46. Question
An attacker impersonates a delivery driver and waits outside of a building. When an employee gains security’s approval and opens the door, the attacker asks the employee to hold the door to gain access to the building. What type of social engineering attack the attacker has performed?
CorrectIncorrect -
Question 47 of 70
47. Question
You have been tasked with implementing a solution to send product offers to consumers’ smartphones when they trigger a search in a particular geographic location, enter a mall, neighborhood, or store. What solution will you implement in order to achieve that?
CorrectIncorrect -
Question 48 of 70
48. Question
The attacker uses a tool named Driftnet to fool both router and workstation to connect to the attacker’s machine, instead of to each other. Then, the attacker is secretly in the middle of all communications. What type of attack is this an example of?
CorrectIncorrect -
Question 49 of 70
49. Question
End-users within an office building report web server connectivity issues. A network administrator troubleshooting the issue notices there is a high CPU load on the server when typing the
grep processor /proc/cpuinfocommand. Which of the following is causing the issue?CorrectIncorrect -
Question 50 of 70
50. Question
Which of the following is the MOST effective way to prevent network security breaches from happening in the workplace?
CorrectIncorrect -
Question 51 of 70
51. Question
PC1 can ping the printer on the Marketing team network but can’t ping the printer on the Sales team network. Assuming you are working on a Windows environment, type the command to get details about the route that packets go through from PC1 to the printer on the Sales team network?
-
C:\Users\ExamsDigest\PC1>
CorrectIncorrect -
-
Question 52 of 70
52. Question
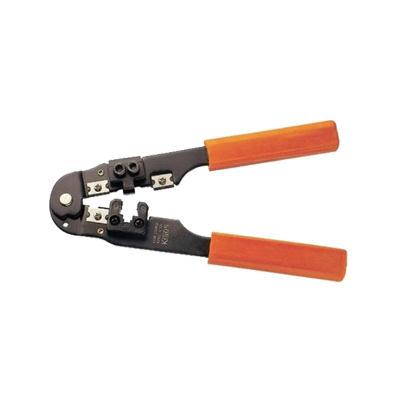
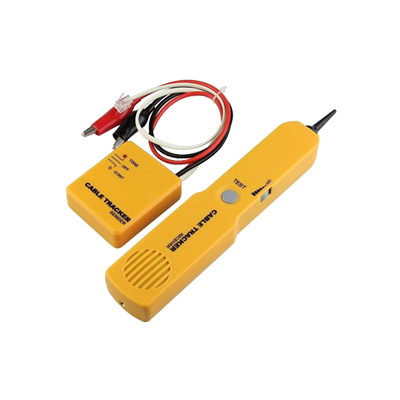
Drag and drop the hardware tools into their respective fields.
Sort elements
- Crimper tool
- Cable tester
- Punchdown tool
- Tone generator
CorrectIncorrect -
Question 53 of 70
53. Question
Which of the following tools can be used to perform manual DNS lookups on a Linux environment? (Select TWO)
CorrectIncorrect -
Question 54 of 70
54. Question
Assuming you are working on a Windows environment. Type the command to discover your IP information, including DHCP and DNS server addresses.
-
C:\Users\ExamsDigest> /all
CorrectIncorrect -
-
Question 55 of 70
55. Question
You just received a new troubleshooting ticket from your co-worker, Peter. He is trying to connect on the internet (wirelessly) but he receives an error message that says “There is an IP address conflict with another system on the network”. Which of the following option will resolve the issue?
CorrectIncorrect -
Question 56 of 70
56. Question
Your co-workers complain about slow network speed whenever they are in the company’s kitchen. Your co-workers use the Wi-Fi in the lobby area without issues. Though the access point (AP) shares the same distance between the kitchen and lobby, the data speed in the former is slower. Which of the following actions should you perform to increase the data speed?
CorrectIncorrect -
Question 57 of 70
57. Question
Users within an office building report network connectivity issues. A network technician troubleshooting the issue asks questions to better understand the situation. Which of the following steps of the CompTIA troubleshooting methodology BEST describes the action the technician takes?
CorrectIncorrect -
Question 58 of 70
58. Question
A technician is called to troubleshoot a client PC that is not connecting to the network. Upon investigation of the TCP/IP settings, it is discovered that a client receives an IP address of 169.254.2.2. Which of the following is the MOST likely issue?
CorrectIncorrect -
Question 59 of 70
59. Question
A network technician is connecting to a switch to modify the configuration. The switch interface Fast Ethernet 0/20 is not enabled, which causes connectivity issues. Which of the following commands does the technician need to use to connect to the switch remotely?
CorrectIncorrect -
Question 60 of 70
60. Question
A network administrator is called to troubleshoot a remote Windows PC using telnet. The administrator first needs to examine the TCP/IP settings on this PC. Which of the following commands should he enter on the workstation to check the TCP/IP settings?
CorrectIncorrect -
Question 61 of 70
61. Question
A network technician is connecting to a Cisco switch to configure the interfaces. The technician first needs to examine the current configuration settings before applying the new changes. Which of the following commands does the technician need to type to display the current configuration?
CorrectIncorrect -
Question 62 of 70
62. Question
A technician is called to troubleshoot a wireless network. Users complain the signal strength level is unacceptable as they aren’t able to connect to the internet anymore. Which of the following -dBm levels the wireless network interface card MOST likely reports?
CorrectIncorrect -
Question 63 of 70
63. Question
Drag and drop the command-line tools into their respective fields.
Sort elements
- nslookup
- ping
- ifconfig
- route
-
Query DNS servers for resource records
-
Check if a networked device is reachable
-
Display your IP address in Linux systems
-
View and manipulate the IP routing table
CorrectIncorrect -
Question 64 of 70
64. Question
You have been tasked with configuring a static route on a Windows workstation. The destination network has an IP of 192.168.60.0 with a subnet mask 255.255.255.0, and the gateway IP is 192.168.0.1. Type the command to complete the task.
-
C:\ExamsDigest\Student_1>
CorrectIncorrect -
-
Question 65 of 70
65. Question
A wireless technician is called to ensure 360-degree wireless coverage within the organization. The technician first examines the antenna type and the place where the antenna is being installed. Which of the following types of antenna should be installed to provide connectivity in all directions?
CorrectIncorrect -
Question 66 of 70
66. Question
What type of cloud services can allow you to increase or decrease IT resources as needed to meet changing demand?
CorrectIncorrect -
Question 67 of 70
67. Question
Nick is a network engineer who is planning to design an organization’s network. The servers (Web, Email, File) should receive static public IP addresses 5.5.5.1, 5.5.5.2, and 5.5.5.3 respectively. The hosts inside the organization should receive IP addresses automatically using DHCP from the range 172.16.0.0 to 172.16.255.255 without being able to access the internet or any service outside of that network. Which of the following IP addressing schema SHOULD be configured for the hosts inside the organization?
CorrectIncorrect -
Question 68 of 70
68. Question
What is the last available address that can be assigned to a host associated with the network located at 72.29.189.2/27?
CorrectIncorrect -
Question 69 of 70
69. Question
What information can you extract having the IP address 172.16.99.45? (Select TWO.)
CorrectIncorrect -
Question 70 of 70
70. Question
A network security engineer is tasked with implementing a solution to allow users from untrusted networks to access the Web Server and the Mail Server while keeping the private network secured and inaccessible. Which of the following does the engineer need to implement to complete the task?
CorrectIncorrect