Time limit: 0
Quiz Summary
0 of 13 Questions completed
Questions:
Information
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading…
You must sign in or sign up to start the quiz.
You must first complete the following:
Results
Quiz complete. Results are being recorded.
Results
0 of 13 Questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 point(s), (0)
Earned Point(s): 0 of 0, (0)
0 Essay(s) Pending (Possible Point(s): 0)
Categories
- Not categorized 0%
-
Unfortunately, you didn’t pass the quiz, but hey, you have unlimited access.😎
Practice makes you perfect! 👊 -
Congratulations! 🥳
You have passed the quiz successfully! You are one step closer to pass the real exam!
We hope to see you again on another certification path.✌️
Good luck with the exam! Stay strong.👊
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- Current
- Review
- Answered
- Correct
- Incorrect
-
Question 1 of 13
1. Question
Given the following URI https://courses.examsdigest.com/ccna, which part is the hostname?
CorrectIncorrect -
Question 2 of 13
2. Question
Match the applications with their well-known port numbers.
Sort elements
- HTTPS
- HTTP
- SSH
- SMTP
- POP3
- DNS
-
443
-
80
-
22
-
25
-
110
-
53
CorrectIncorrect -
Question 3 of 13
3. Question
Which of the following options are things that a standard IP ACL could be configured to do? (Choose two answers.)
CorrectIncorrect -
Question 4 of 13
4. Question
Type the wildcard mask that matches all IP packets in the subnet 46.45.44.0, and mask 255.255.255.0.
-
. . .
CorrectIncorrect -
-
Question 5 of 13
5. Question
Type the access-list command that permits all packets sent from hosts in subnet 14.15.16.0/24. Use the ACL number 50 for the ACL rule.
CorrectIncorrect -
-
Question 6 of 13
6. Question
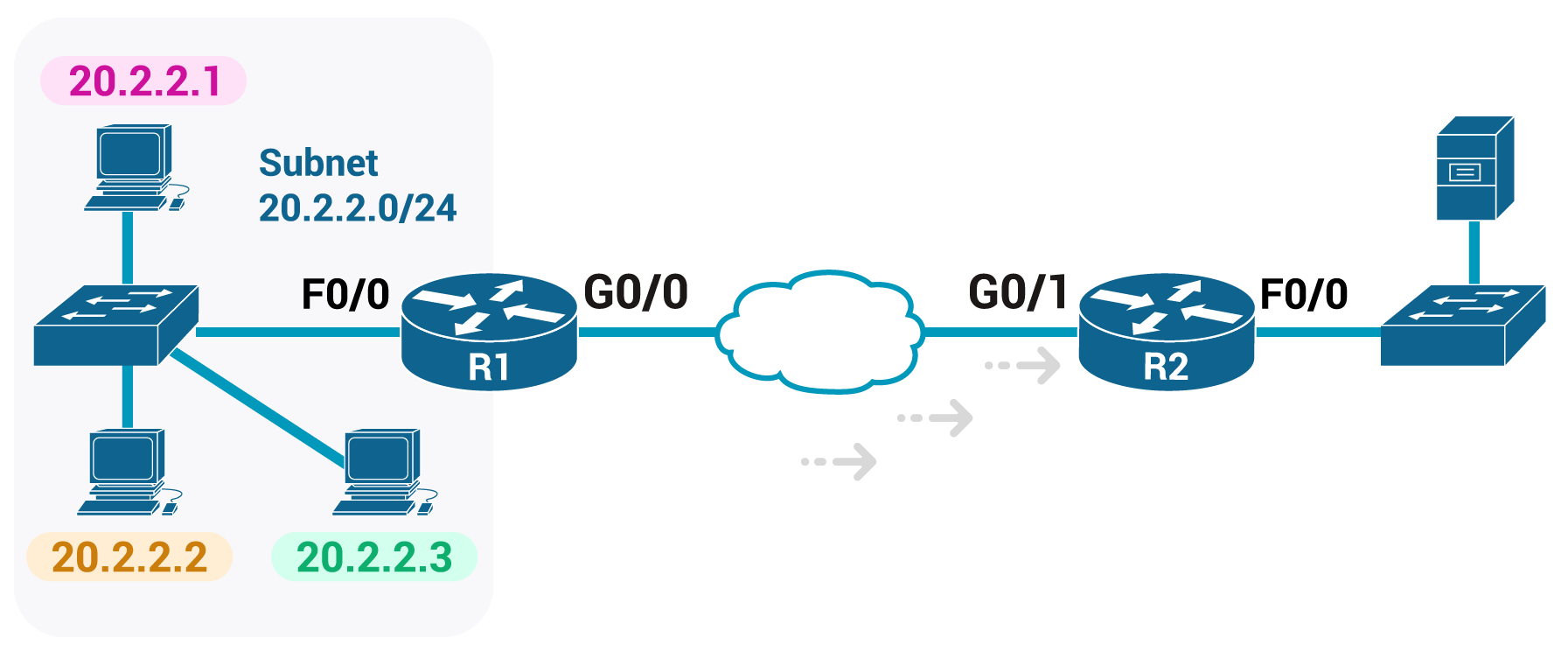
The senior network engineer assigns you a task that requires ACL configuration. He provides the following diagram and the requirements below:
1) Enable the ACL inbound on R2’s G0/1 interface.
2) Permit packets coming from the host with IP 20.2.2.1
3) Deny packets coming from the rest subnet 20.2.2.0/24
4) Permit packets coming from a network with subnet 155.165.0.0/16Now you are responsible to configure the R2 using the ACL standard number 1.
-
R2#
Enter configuration commands, one per line. End with CNTL/Z.! Permit packets coming from the host with IP 20.2.2.1
R2(config)#! Deny packets coming from the rest subnet 20.2.2.0/24
R2(config)#! Permit packets coming from a network with subnet 155.165.0.0/16
R2(config)#! Enable the ACL inbound on R2’s G0/1 interface.
R2(config)#
R2(config-if)#
R2(config-if)# ^Z
R2#
CorrectIncorrect -
-
Question 7 of 13
7. Question
Your task is to type a one-line standard ACL that matches the following criteria. All access-list commands use the number 1 in the command.
-
Criteria #1: Permit packets from 186.33.2.3
ACL command #1:
Criteria #2: Permit packets from hosts with 56.57.2 as the first three octets
ACL command #2:
Criteria #3: Permit packets from hosts with 56.57 as the first two octets
ACL command #3:
Criteria #4: Permit packets from any host
ACL command #4:
CorrectIncorrect -
-
Question 8 of 13
8. Question
Match the access-list statements with their logic.
Sort elements
- access-list 101 deny udp any gt 10455 host 30.3.3.3 eq 25
- access-list 101 deny udp any lt 10455 host 30.3.3.3 eq 25
- access-list 101 deny udp host 30.3.3.3 gt 10455 any eq 25
- access-list 101 deny udp host 30.3.3.3 lt 10455 any eq 25
-
Deny packets with a UDP header, any source IP address with source port greater than 10455, a destination IP address 30.3.3.3 and a destination port equal to 25.
-
Deny packets with a UDP header, any source IP address with source port less than 10455, a destination IP address 30.3.3.3 and a destination port equal to 25.
-
Deny packets with a UDP header, a source IP address 30.3.3.3 and a source port greater than 10455, any destination IP address 30.3.3.3 with destination port equal to 25.
-
Deny packets with a UDP header, a source IP address 30.3.3.3 and a source port less than 10455, any destination IP address 30.3.3.3 with destination port equal to 25.
CorrectIncorrect -
Question 9 of 13
9. Question
One of the differences between named and numbered ACLs is that named ACLS using ACL subcommands, not global commands, to define the action and matching parameters.
CorrectIncorrect -
Question 10 of 13
10. Question
Which of the following commands display the configuration of an IPv4 ACL, including line numbers? (Choose two answers.)
CorrectIncorrect -
Question 11 of 13
11. Question
Your task is to type a one-line extended ACL that matches the following criteria. All access-list commands use the number 101 in the command.
-
Criteria #1: Permit packets from web client 65.5.5.5, sent to a web server in subnet 65.5.6.0/24
ACL command #1:
Criteria #2: Permit any and every IPv4 packet.
ACL command #2:
Criteria #3: Permit any tcp packet from Telnet server 80.80.80.0/24’s subnet, sent to any host in the subnet 90.90.90.0/24.
ACL command #3:
CorrectIncorrect -
-
Question 12 of 13
12. Question
The ACL 55 on R1 has four statements, with address and wildcard mask values as follows:
20.0.0.0 0.255.255.255
20.20.0.0 0.0.255.255
20.20.20.0 0.0.0.255
2.2.2.0 0.0.0.255If a router tried to match a packet sourced from IP address 20.20.20.20 using this ACL, which ACL statement does a router consider the packet to have matched?
CorrectIncorrect -
Question 13 of 13
13. Question
Given the following access-list command access-list 2 permit 192.168.4.0 0.0.0.255.
Which of the following options is the exact range of IP addresses, matched by the command?
CorrectIncorrect